OWASP A2 - Broken Authentication and Session Management - GBHackers - Latest Cyber Security News | Hacker News

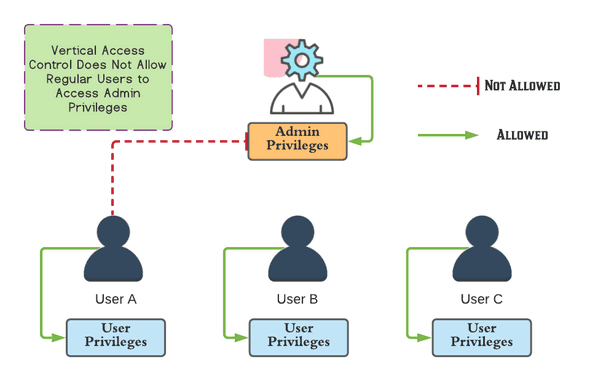
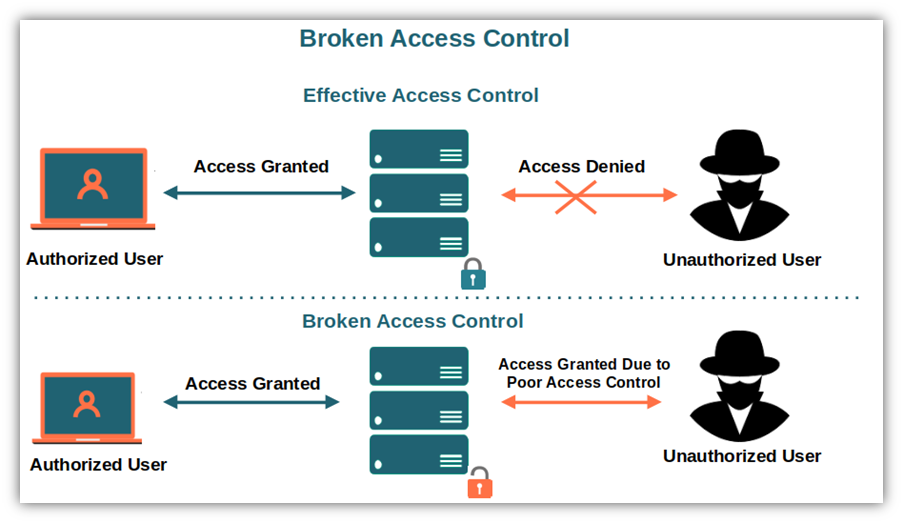
What is broken access control? - OWASP Top 10: #1 Broken Access Control and #2 Cryptographic Failures Video Tutorial | LinkedIn Learning, formerly Lynda.com

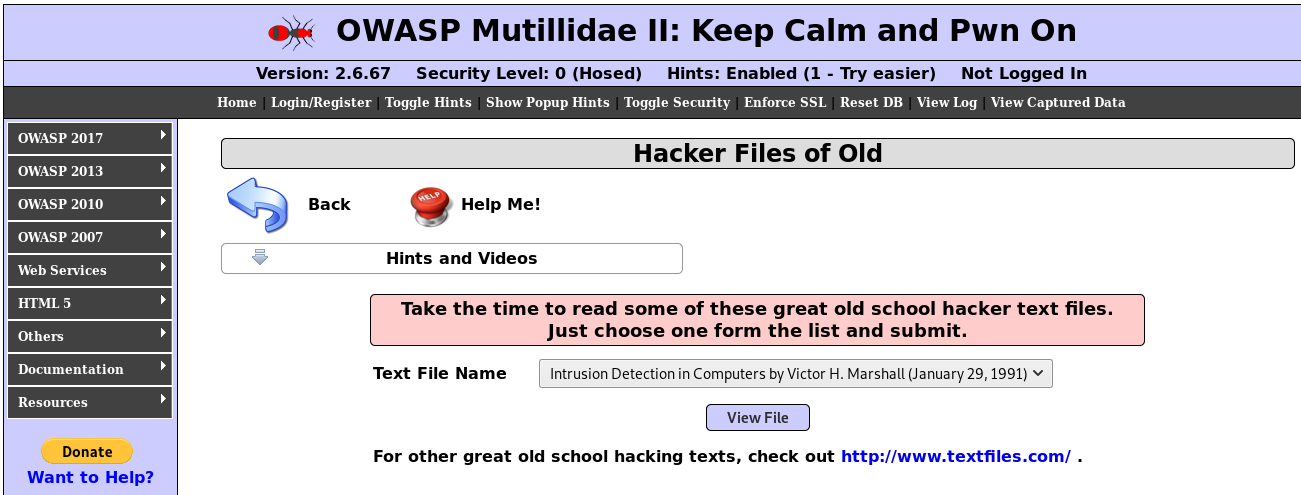
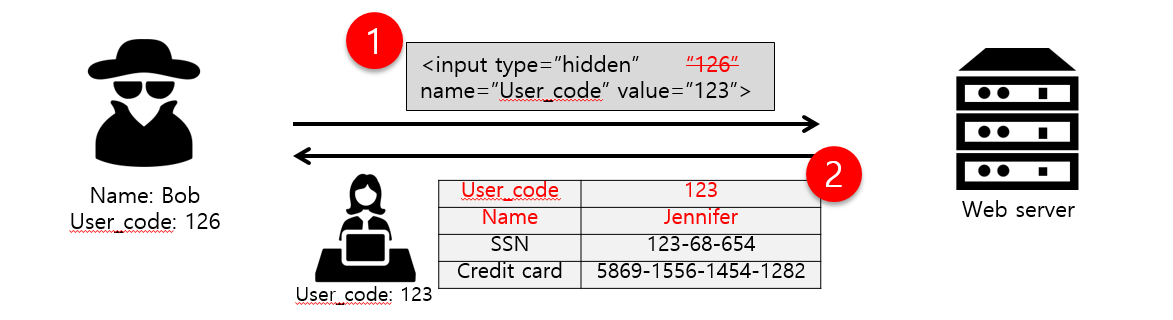
How to Catch Broken Access Control Security Vulnerabilities in Code Review Part 2 | PullRequest Blog